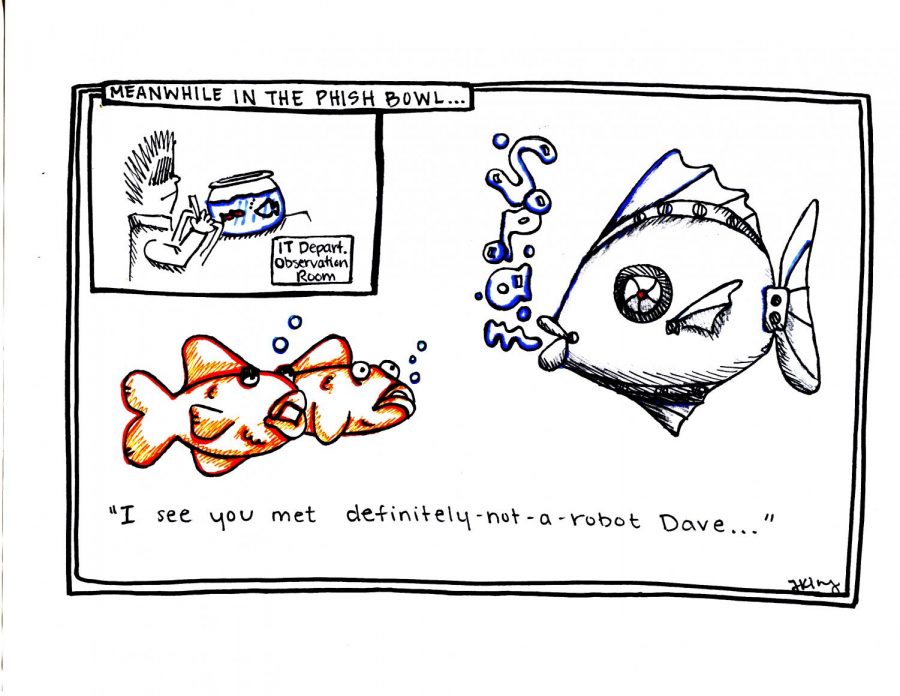
IT department releases idea to prevent phishing
August 31, 2016
GO PHISH
In an effort to protect students from phishing emails, the Information Technology department at WKU has a created the Phish Bowl where students can view recent emails that have been sent by scammers.
The Phish Bowl is designed to help people identify these emails. An email sent from Greg Hackbarth, director of enterprise systems, to all faculty, staff and students, recommends that recipients of mysterious email go to the Phish Bowl. The Phish Bowl contains a list of various emails that have been sent to members of the WKU community.
“If the email is on the Phish Bowl, it is a confirmed phishing scam, and you can delete it,” the WKU IT department said in the email.
According to Phishing.org, a website dedicated to providing information on how to avoid phishing emails, phishing is defined as a “process where a targeted individual is contacted by email or telephone by someone posing as a legitimate institution to lure the individual into providing sensitive information.” This information is then used to access an individual’s accounts which can result in financial loss or identity theft.
If the email is not on the Phish Bowl, then the individual can forward it to [email protected] or contact the IT department.
The Twitter account for the IT department, @wkuIT, also posts images of phishing emails that have been tweeted by other members of the WKU community.
Many of the phishing emails are sent from a WKU address such as @topper.wku.edu and @wku.edu.
In an email Hackbarth said phishers are able to gain access to these email addresses in a number of ways.
“They gain knowledge of the existence of a topper account in various ways, either by discovering topper addresses published on the web or looking up accounts in the WKU directory,” Hackbarth said. “Once they gain access to a topper account, they can look up other user addresses there.”
Hackbarth said the IT Department has considered the idea to make WKU addresses harder to find; however, doing so would affect the accessibility of contact information.
To protect themselves, faculty, staff and students must identify phishing emails they receive.
According to the IT department’s website, these emails can be identified in multiple ways. Many of these emails are designed to appear to alert individuals to problems with an account, and they may appear suspicious or be labeled “urgent” or “immediate action.”
Other emails often contain attachments. The IT department recommends not opening any attachments that an individual did not anticipate receiving. It is also important to look at the address of the sender. Emails sent from unknown addresses may have been sent by scammers.
Hackbarth said the idea for the Phish Bowl was a collaboration of the IT staff in the Technical Support Services.
“They basically saw a need for the service, but they also saw another use for the emails that are reported to [email protected] and saw a use for Google Analytics, which is used to track the various marketing campaigns that drive people to the site,” Hackbarth said.
The Phish Bowl was designed to help educate the campus about these scams. The IT department has taken other steps to educate the public before; however, this effort was designed to be slightly different.
“The main point was to raise phishing awareness through clever and increased marketing,” Hackbarth said. “It will hopefully reach a broader audience than the other educational methods we have employed, and of course we’re able to track the effectiveness of our marketing efforts.”
So far, Hackbarth said he believes the Phish Bowl has been successful. The email account, which has existed for several years, receives around a dozen emails everyday. Many of them contain the same email.
“A lot of reports are duplicates, so only the unique examples are posted to the Phish Bowl,” Hackbarth said.
During the year, the reporting of these emails tends to cycle.
“In the first week of this semester, we had about 200 reports of compromised accounts,” Hackbarth said. “There are over 30,000 active TopperMail accounts, and another few thousand faculty/staff accounts.”
Gordon Johnson, vice president of the IT department, said in an email that WKU is not alone in dealing with phishing.
“All universities are seeing increases in phishing activity because faculty, staff, and student email address are publicly available in university environments,” Johnson said.
Phishing is also not a new problem for the university.
“Phishing has been going on for almost as long as we’ve had email, but as WKU has grown and as these scams have become more popular, the number of phishing attempts directed toward WKU users has increased,” Hackbarth said.
Throughout this time, the most powerful information a hacker can obtain is the login information for an email. Most websites provide the option to receive an email containing a temporary password if an individual happens to forget the login for a particular account.
“If a hacker has your email account, they essentially have all of your accounts,” Hackbarth said.
In addition to gaining access to most of an individual’s accounts, the hacker is also able to gain access to an individual’s contacts by posing as someone those contacts trust: the individual.
If an individual does respond to a phishing email, Hackbarth said the most important step is to act quickly and immediately change passwords. If the account is a WKU account, the individual can also contact the IT Helpdesk and going to the IT security website to report the incident.
“Those are the most important steps, but there are additional tips on the IT Security site if you are concerned about protecting your identity or credit,” Hackbarth said.
Reporter Emma Collins can be reached at 270-745-6011 and [email protected]. Follow her on Twitter at @CollinsEmmaM.